Cyber Security Assessment Frameworks
16 Nov 2022
Cyber security assessment frameworks

Improving cyber security remains a top priority for small businesses, SMBs, SMEs and enterprises alike.
Cyber attacks in the UK are becoming more common for both smaller and larger businesses, whereas global losses from cyber crime are expected to reach $10.5 trillion by 2025.
To combat cyber crime, national and international institutions have produced cyber security frameworks to unify organisations under professionally developed standards. Frameworks guide cyber security risk assessment, providing a roadmap towards more effective controls and risk mitigation strategies, and are also key part of cyber risk management.
With a solid cyber security risk assessment in place, organisations can confidently move forward with the knowledge that their data and critical assets are secure. Frameworks are integral to the assessment process.
This is an introduction to cyber security assessment frameworks.
What is a cyber security assessment framework?
A cyber security assessment framework provides organisations with a means to systematically analyse and review their digital infrastructure and operations to control and mitigate cyber security risks.
Applying a cyber security assessment framework helps businesses address the following core threats:
- Ransomware.
- Distributed denial of service (DDoS) attacks.
- Data breaches.
- Malware.
- Phishing.
- Account takeover.
- Social engineering attacks.
- Software supply chain attacks.
- Advanced persistent threats (APT).
- Man-in-the-middle attacks (MitM).
A cyber assessment framework is multi-faceted and assesses everything from governance and risk management to data and system security, asset management, detection and incident/crisis response.

Above: Businesses can apply a cyber assessment framework to virtually every industry in our highly-digitised world
While prevention and threat detection are vital to prevent risks from developing in the first place, assessments also look at incident response, communications and disaster recovery.
Many guidelines are long, highly detailed, and don’t apply to every organisation. However, there are fundamental similarities. All in all, a cyber assessment framework addresses the following core elements:
- Identify: Potential threats, vulnerabilities and current IT governance are assessed and analysed to achieve essential cyber security goals.
- Protect: Identifies data security and system security strategies to protect assets and data at rest and in transit.
- Detect: System and network monitoring to identify threats via anomaly detection, traffic monitoring, zero-day exploit detection, etc. Staff training to reduce social engineering and phishing.
- Response: Incident management, reporting to authorities and crisis communications.
- Recover: Loading backups, dealing with data loss and reputational damage, etc.
Cyber security frameworks support laws and regulations, such as the EU Security of Network and Information Systems Directive (NIS Regulations) and the General Data Protection Requirements (GDPR). They act as a valuable resource for businesses that belong to critical infrastructure or regulated sectors (e.g. UK Critical National Infrastructure).

Above: Implementing a cyber security assessment framework supports cyber security regulation
What are the common cyber security assessment frameworks?
The choice of cyber security assessment framework varies with the business, sector, industry and other factors. Some of the most popular assessment frameworks include:
- NIST CSF (NIST Cyber Security Framework) - the National Institute of Standards and Technology Framework for Improving Critical Infrastructure Cybersecurity. This is a voluntary framework for businesses that don’t qualify as US federal government agencies, for whom it’s mandatory. There is also the NIST Risk Management Framework (NIST RMF) which is mandatory for federal agencies to comply with the Federal Information Security Modernization Act (FISMA)
- The NIST Special Publication 800-53, which provides security and privacy controls and a risk assessment framework for federal US IT systems except for systems related to national security. 800-53 contains controls for bringing organisations in line with FISMA
- NSCS CAF - the UK National Cyber Security Centre Cyber Assessment Framework. The NSCS CAF is naturally angled towards organisations operating in the UK and is designed to support UK cyber regulation.
- ISO/IEC 27001 and 27002 - the International Standards Organization (ISO) frameworks. These are very widely recognised international benchmarks for IT and cyber security. Often used outside the US by businesses to give assurance to customers and clients that a company practises a high level of cyber security. To learn more see our guide on how to get ISO 27001 certified.
- CIS CSC - the Center for Internet Security CIS Critical Security Controls. Formerly named the SANS Critical Security Controls (SANS Top 20), this is an international framework developed by a non-profit group.
- PCI DSS - the Payment Card Industry Data Security Standard. Developed by MasterCard, Discover Financial Services, Visa, JCB International and American Express, this forms mandatory guidelines for organisations that process, store or transmit payment card information.
- SOC2 - System and Organization Controls 2. a voluntary standard for service organisations that handle data, developed by the American Institute of CPAs (AICPA). Often used in the US by businesses to give assurance to customers and clients that a company practises a high level of cyber security.
What is the best cyber security assessment framework to use?
Most organisations are free to apply the frameworks and guidelines that best fit their operations and objectives.
Cybersecurity assessment frameworks are fundamentally similar, but some have been developed for specific industries and critical infrastructure (e.g. PCI DSS for the payment and financial services industries). There are both national frameworks (e.g. the USA’s NIST CSF and the UK’s NSCS CAF) and international frameworks (e.g. CIS CSC and ISO/IEC 27001 and 27002).
On balance, the CIS Critical Security Controls framework and ISO 27001 are perhaps the most universally applicable assessment frameworks and controls. Thousands of global organisations utilise the CIS framework. They’re endorsed by the European Telecommunications Standards Institute (ETSI) and the UK Centre for the Protection of National Infrastructure (CPNI).
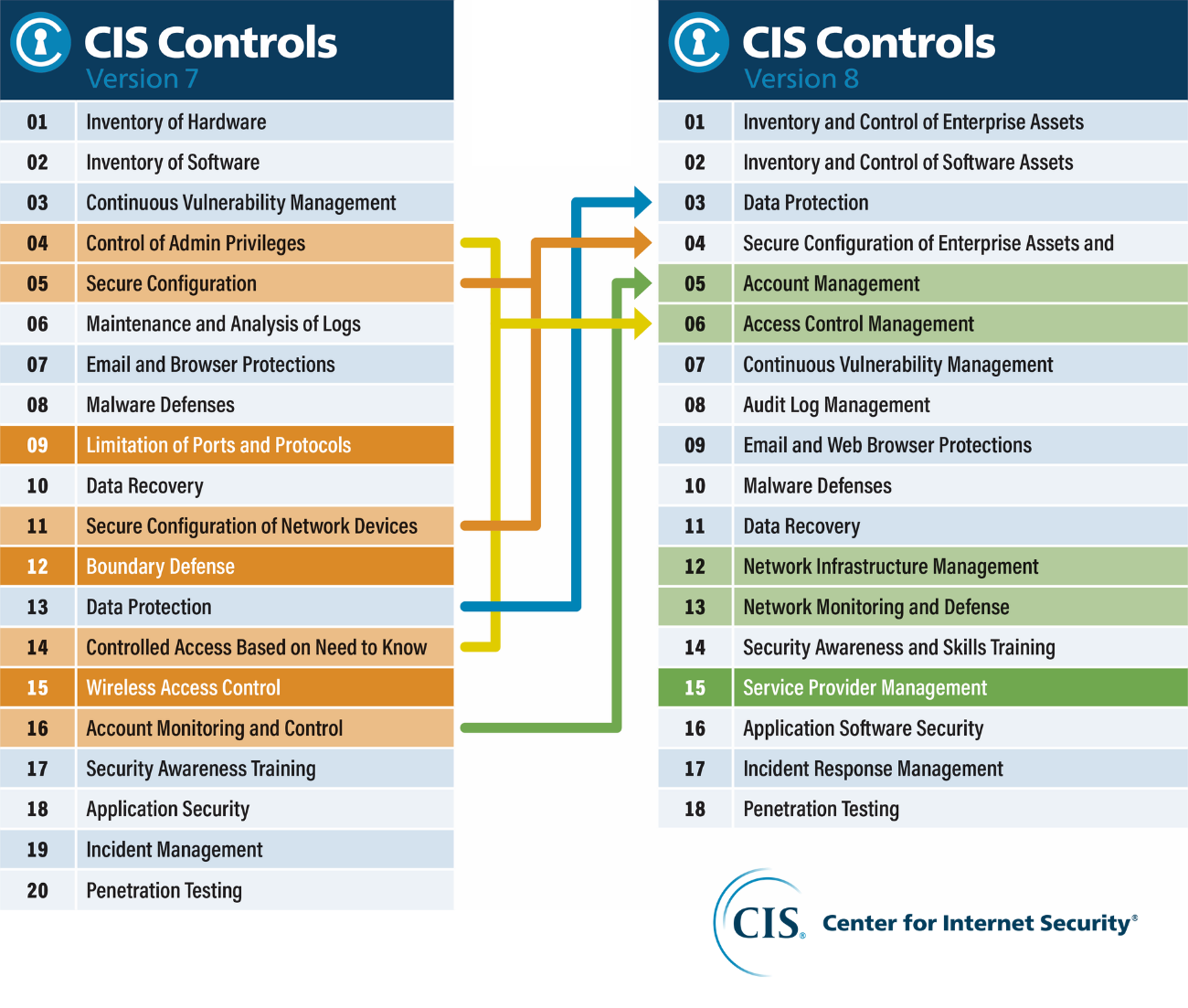
Above: CIS Controls Version 8
The CIS publish mappings of the Critical Security Controls onto other frameworks and controls such as NIST CSF and ISO 27000. This, in principle, makes CIS one of the most comprehensive frameworks available.
In addition, SOC2 and ISO 27001 are widely used by organisations to give clients assurance that cyber security is being taken seriously and is properly managed. ISO 27001 is generally used for this purpose in Europe, and SOC2 in the US.
Our Cyber Health Checks typically use a mixture of the CIS Critical Security Controls framework and ISO 27001, which gives extensive coverage and can be tailored to the requirements of businesses in every sector.
The ideal cyber security framework varies from business to business
Overall, every organisation with substantial digital operations should conduct cyber security assessments and choose a framework applicable to their industry, requirements and business objectives.
Applying frameworks and guidelines and addressing issues builds resilience and enables digital transformation.
Nicolson Bray offers bespoke cyber security risk management and review services catering to organisations across multiple industries and industries.
We help businesses build secure and resilient architectures and engineer security solutions that address complex objectives. Contact us today to find out how we can help you transform your organisation’s cyber security.
